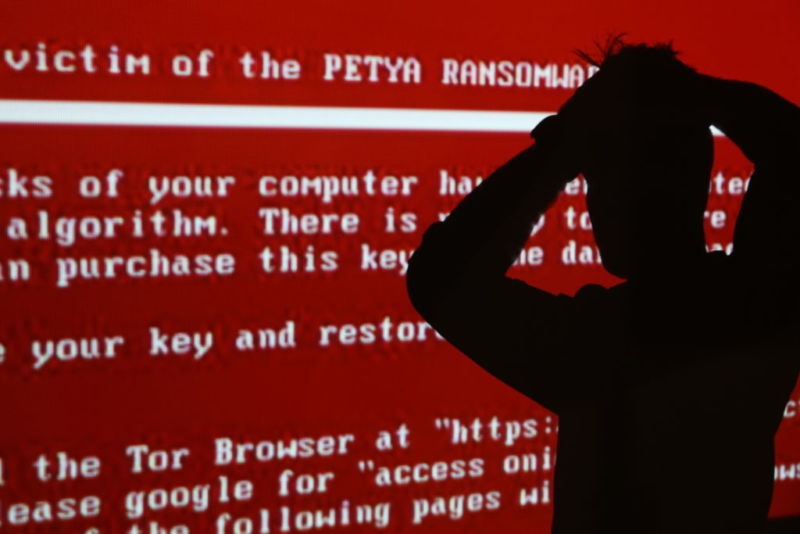
What To Do If You Get Threatened With Ransomware
Ransomware is one of the wilder forms of malware attacks circulating the technology industry today. The concept is simple: a hacker and a victim get into a malicious game of “monkey in the middle,” where the hacker holds sensitive files hostage until the victim pays a ransom, usually in the form of an online payment.
Although it sounds scary, ransomware is a lot like bullying. The power sits in the bully’s – or hacker’s – hands until you take steps to remove that power. When your files are protected, a hacker can’t hold them hostage in return for a ransom demand.
Let’s take a look at some of the common kinds of ransomware and what to do if your or your business’s files are ever threatened.
What is ransomware?
Ransomware can follow a wide range of patterns and symptoms, ranging from annoying to catastrophic. What sets ransomware aside from other types of malware is that all ransomware involves some type of ransom demand. There are five main types:
- Lockers are typically the first thing people think of when they hear the term “ransomware.” These attacks target computer systems and lock their owners out completely. The hacker then can demand a sum of money or other payment in exchange for restoring access to the system.
- Scareware. Have you ever seen a pop-up that told you your computer or phone was infected with millions of viruses and needed an expensive cleanup NOW? If it demanded money, or if it wasn’t a trusted antivirus program you installed yourself, it might have been scareware. Scareware imitates antivirus and cleaning tools to “scare” victims into paying for an expensive “cleanup.” Unfortunately, the cleanup often involves downloading more untrustworthy programs onto your computer, which demand additional payments for removal or cleanup, and the whole cycle continues.
- Crypto malware. This form of ransomware is called “crypto” because it demands payment in cryptocurrency. Crypto malware exploits CPU cycles (what people use for cryptomining, or collecting cryptocurrency like Bitcoin) to make multiple copies of itself, encrypt system files, and otherwise lock down access to a computer. Then, the hacker demands payment in the form of Bitcoin or another cryptocurrency.
- Ransomware as a Service (RaaS). RaaS is a bit of a strange concept, because it involves approaching hacking like a business. A hacker can offer anonymous hosting, payment processing, or encryption/decryption services for other hackers’ ransomware programs in exchange for a share of the payment. While the person offering RaaS isn’t directly hacking into people’s computer systems, they host the programs and servers that make the damage possible.
- Doxware (or leakware). Do you have sensitive data you don’t want publicly available online? Doxware targets people and business’s privacy concerns by threatening to publish private data, like photographs, bank info, and credit card numbers, in spaces where other hackers (or the general public) can access them with ease. It makes sense why so many people panic and pay ransoms to keep sensitive data from going public.
What should I do if I get threatened with ransomware?
The most important thing is to never pay the demanded ransom. There is no guarantee that paying the ransom will make the hacker restore access to your files, choose not to post things online, or otherwise do anything they said they would. In fact, like many bullying scenarios, caving to the hacker’s demands could make them more likely to demand a higher payment.
It’s a good idea to install trusted antivirus and antimalware, and keep them updated and running at all times. A lot of malware wriggles its way into computer systems through infected email attachments, downloads, or programs. A good rule of thumb is, “If you don’t know or trust the source, don’t click.” Delete those questionable emails, and never install a program or open an attachment that requires you to enable macros or disable your antivirus. These extra protections will help reduce your risk of a ransomware attack, but they can’t eliminate it completely.
In fact, the only surefire protection from a ransomware attack is a 100% backup system. Cloud computing, file sharing, and other systems that save progress can give you a chance to restore files to a point before they were encrypted, giving you access again while locking the hacker out.
A dedicated managed service provider like GTS will put procedures in place to give your business and your files the utmost protection possible. At Grand Technology Solutions, we offer remote monitoring and management subscriptions that keep your security up to date, and monitor all activity for potential breaches or issues 24/7/365.
Is your business’s security up to snuff? Give us a call today at (904) 606-6011 to learn more about what GTS can do to protect you and your business from ransomware attacks.